Cyberattacks on SolarWinds and Oldsmar: CEO Interview Series, John Livingston, Verve Industrial Protection

Between the SolarWinds cyberattack and the smaller, but no less frightening, Oldsmar attack on a water treatment plant near Tampa Bay, Florida., cybersecurity has been front and center in the news. But these two cyberattacks […]
Four ways to achieve physical and cybersecurity integration in industrial operations

Cybersecurity is a relatively recent top concern for industrial enterprises. A number of high-profile security incidents like the hacking of a Florida water treatment plant, have brought the topic into public scrutiny, but the issue […]
Tabletop card game about cybersecurity teaches online fundamentals

The Hackers’ Epoch: The Cybersecurity Card Game by Scruffy City Games helps students understand online threats and teaches them fundamental terms they’ll need to learn. After playing the game, when they read a news article […]
Four OT, ICS security patching lessons to consider

Having comprehensive list of security-related patches by using operational technology (OT)-specific patching tools to gather complete software, vulnerability, and security patching information sounds simple. Information technology (IT) security professionals will tell users to scan it […]
Extend IT security to the plant floor

Cybersecurity is critical as information technology (IT) and operations technology (OT) converge, which is the first step in making the transition between the two sides almost seamless.
Four ways to sharpen building system technologies

IoT and intelligent management systems have revolutionized the capabilities of our buildings by enabling better automation and increasing efficiencies for better overall building health
eBook: Threats and Vulnerabilities

Featured articles in this eBook include stories on cybersecurity for IIoT robots, cybersecurity asset updates and using cybersecurity to improve tomorrow’s manufacturing operations.
Compensating controls in ICS cybersecurity
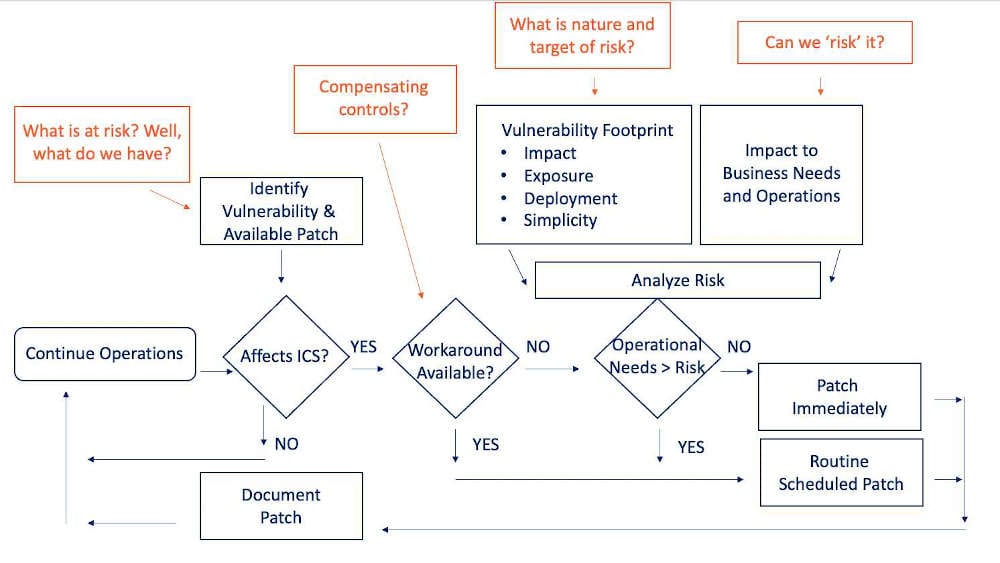
Most operational technology (OT) environments use scan-based patching tools, which are pretty standard but not overly insightful to show us what assets we have and how they are configured. What is really needed is robust […]
When remote monitoring and control becomes essential for manufacturing operations

The COVID-19 pandemic is forcing companies to adjust their business practices and settle to a new normal. See four tips on how edge computing and the Industrial Internet of Things (IIoT) can help companies adjust.
Industrial controller cybersecurity best practices
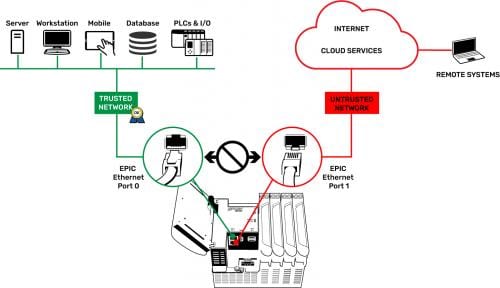
Protecting industrial automation systems is easier when controllers offer built-in cybersecurity features.




