The vulnerability of U.S. critical national infrastructure was again thrown into sharp relief when a ransomware attack shut down a pipeline that provides the East Coast with nearly half of its diesel, gasoline and jet fuel. The cyberattack, which targeted the Colonial Pipeline, the largest refined-products pipeline in the U.S., is the latest in a string of high-profile hits on critical infrastructure that have included everything from the Oldsmar water treatment facility in Florida to the Washington, D.C., police department to the SolarWinds attack that impacted several key government agencies.
Colonial released a May 7 statement saying it “learned it was the victim of a cybersecurity attack and has since determined that the incident involved ransomware. Quickly after learning of the attack, Colonial proactively took certain systems offline to contain the threat. These actions temporarily halted all pipeline operations and affected some of our IT systems, which we are actively in the process of restoring.”
Georgia-based Colonial chose to shut down its pipeline operations as a precautionary measure and to ensure that the ransomware couldn’t migrate from business computer systems to those that control the pipeline, said White House Homeland Security Adviser Elizabeth Sherwood-Randall in a May 10 news conference. The company is working with private cyber consultants FireEye/Mandiant to assess preliminary damage and to determine when it’s safe to bring the pipeline back online.
“Thus far, Colonial has told us that it has not suffered damage and can be brought back online relatively quickly but that safety is a priority given that it has never before taken the entire pipeline down,” Sherwood-Randall said.
Russian cyber gang behind the Colonial hack
Though details are still emerging, the FBI confirmed that a relatively new but savvy Russian cybercriminal gang, known as DarkSide, is behind the breach. Their typical method of attack is to take data hostage – they stole nearly 100 gigabytes of Colonial data – threaten to make it public and demand a hefty fee for its return.
“The FBI identified the ransomware as the DarkSide variant, which they’ve been investigating since October of last year,” said Ann Neuberger, deputy national security adviser for cyber and emerging technologies. “It’s a ransomware as a service (RaaS) variant, where criminal affiliates conduct attacks and then share the proceeds with the ransomware developer.”
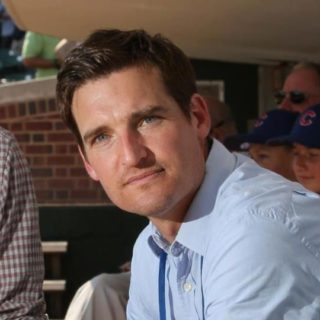
According to NBC News, early indications suggest this was a criminal extortion scheme and not a Russia-backed nation-state attack. Still, this is an alarming example of just how vulnerable the U.S. critical national infrastructure is to sophisticated bad actors. And it could be the preamble to a prolonged cyber war between global powers, said Wayne Dorris, a certified information systems security professional (CISSP) and business development manager for cybersecurity with Axis Communications.
The Colonial cyberattack certainly captured the attention of the Biden administration, which has been working to secure national cybersecurity since the SolarWinds attack made headlines shortly before they took office in December 2020. Following that breach, the White House formally blamed Russia’s Foreign Intelligence Service and imposed new economic sanctions on the country.
“If I was Russian and I had these economic sanctions, this is exactly what I would be doing,” Dorris said. “It was pretty clear with Colonial, DarkSide had pointed out that there were certain organizations they thought were ethically good, and funny how they were all companies that were sympathetic to Ukraine and Russia. When you ask why this happened, I think this is what’s going to become the norm in response to those sanctions.”
Why attack critical national infrastructure?
The Colonial pipeline runs from the Gulf Coast in Texas up to Linden, New Jersey, and is responsible for 45% of all fuel consumed on the East Coast. According to the company website, Colonial transports 100 million gallons of fuel, or 2.5 million barrels per day — including gasoline, diesel fuel, home heating oil, jet fuel and fuels for the U.S. military — daily through 5,500 miles of pipe.
“The DarkSide ransomware attack on the Colonial Pipeline highlights the increasing risk cybercriminals pose to critical national infrastructure,” said John Vestberg, co-founder and CEO of Clavister, a Sweden-based cybersecurity company. “[Critical national infrastructure], such as oil and gas, is a prime target for these ransomware gangs — systems are underpinned by myriad complex information and operational technology devices and so the consequences if these are infiltrated can be devastating. Attacks on [critical national infrastructure] risk become the norm if action is not taken.
“A proactive, rather than reactive, approach is needed. Using predictive analytics and tools like AI (artificial intelligence) or ML (machine learning), for example, we can see malware morphing and behaving in certain ways and catch it sooner. The DarkSide attack should serve as a warning; [critical national infrastructure] systems are becoming more sophisticated and technical — especially as we enter the era of 5G, which we will soon rely on. Going forward, countries cannot afford to have any weak spots and must step up their cybersecurity solutions to support the technology used,” said Vestberg.
While critical national infrastructure targets can be appealing to hackers because of their obvious national importance, which can result in a tidy profit, oil and gas pipelines present their own set of problems from a cybersecurity perspective.
“Oil and gas also runs energy production, so if I’m a hospital, it’s got to run on oil and gas or electricity,” Dorris said. “Particularly now with COVID, if I take oil and gas out, there’s a problem. They recognize that if people can’t get oil or gas, its long-term effect on the ability to produce power and to just keep things rolling along that we expect every day [is hampered]. If I don’t have enough gas, or fuel gets really expensive, then food doesn’t get to the stores, vaccines don’t get to the hospitals.”
Pipeline cybersecurity also lags behind that of other energy sectors, said John Cusimano, vice president of aeCyberSolutions, a South Carolina-based company that has been working in industrial cybersecurity since 2014.
“A common gap in the pipeline industry is the lack of segmentation of the pipeline supervisory control and data acquisition (SCADA) networks, which are the networks that connect the pipeline control center to every terminal, pumping station, remote isolation valve and tank farm along the pipeline,” Cusimano said. “These are very large networks covering extensive distances, but they are typically flat from a network segmentation standpoint. This means that once someone gains access to the SCADA network, they have access to every device on the network. While pipeline SCADA networks are typically separated from the company’s business information technology (IT) networks with firewalls, by design those firewalls pass some data between the networks.
“The other big challenge with securing pipeline SCADA networks is that they branch into every facility along hundreds of miles of pipeline. Some of those facilities are in very remote places with little to no physical security, meaning that if an attacker breached the security of one of those facilities, they could gain access to the network,” said Cusimano.
Government response to the Colonial attack
President Biden was briefed on the Colonial matter in a series of emergency meetings the weekend following the attack and convened an interagency team that includes the Department of Energy, the Department of Homeland Security Cybersecurity and Infrastructure Security Agency (CISA), the FBI, the Department of Transportation, the Department of the Treasury, the Department of Defense and other agencies.
CISA is preparing a release to go to the broader infrastructure community to ensure it has visibility into the ransomware attack and is taking appropriate measures to protect its networks. The goal is to avoid supply disruptions or a spike in gas prices heading into the summer travel season.
“This weekend’s events put the spotlight on the fact that our nation’s critical infrastructure is largely owned and operated by private-sector companies,” Sherwood-Randall said. “When those companies are attacked, they serve as the first line of defense, and we depend on the effectiveness of their defenses. To improve the cybersecurity of our critical infrastructure, the Biden administration has already launched a high-priority initiative to collaborate with our private-sector partners to harden our defenses and to build our nation’s resilience.”
According to Commerce Secretary Gina Raimondo, who appeared on CBS’s “Face the Nation” May 9, the Energy Department is currently leading the government response to the attack and trying to help Colonial get all its systems back online as soon as possible.
“We are working closely with the company, state and local officials to make sure that they get back up to normal operations as quickly as possible and there aren’t disruptions in supply,” she said on the program. “Unfortunately, these sorts of attacks are becoming more frequent. They’re here to stay.”
Dorris lauded Colonial for being proactive and taking its systems offline. If a company doesn’t do the necessary forensic work following a cyberattack, it’s difficult to determine the true extent of that attack. Even if companies have a solid backup, it’s essential to ensure that the backup doesn’t still have malware in it.
“Sometimes with ransomware, it may have been there for a while, so now your backup has the ransomware too,” Dorris said. “When you restore, you’re just restoring to the problem. It’s important to run scans on the things you’re backing up to know that your backup is actually clean too.
“It’s a complex environment. All I can say is this is just the tip of the iceberg. Because of all these things, like the sanctions, I think we’re going to be seeing more and more attacks across oil and gas, power production, hospitals, anything that’s critical infrastructure. I think this is just a sign of more attacks to come.”
Do you have experience and expertise with the topics mentioned in this article? You should consider contributing content to our CFE Media editorial team and getting the recognition you and your company deserve. Click here to start this process.