On May 27, the United States Department of Homeland Security (DHS) announced its initial regulatory response to the Colonial Pipeline ransomware attack. As the Security Directive highlighted, this is only the first step in what is likely to be a much more robust set of regulatory changes to improve the cyber security of the nation’s critical pipeline infrastructure.
This first directive has significant implications for pipeline operators. Not only does it require disclosure and reporting of incidents, but importantly makes what was a set of voluntary cyber security measures mandatory and auditable. This begins what will likely become a more rigorous compliance regime for pipeline operators.
What is in the May 27 Security Directive?
DHS and the Cybersecurity and Infrastructure Security Agency (CISA) released the Pipeline Security Directive. “The cybersecurity landscape is constantly evolving and we must adapt to address new and emerging threats,” said Secretary of Homeland Security Alejandro N. Mayorkas. “The recent ransomware attack on a major petroleum pipeline demonstrates that the cybersecurity of pipeline systems is critical to our homeland security. DHS will continue to work closely with our private sector partners to support their operations and increase the resilience of our nation’s critical infrastructure.”
The order has three components.
1. Report confirmed and potential cybersecurity incidents to the DHS Cybersecurity and Infrastructure Security Agency (CISA)
This requires that pipeline companies build an incident response capability, which is included in the recommended cyber security elements of the original DHS May 2018 security release. This order adds the requirement to share any cyber incidents with CISA
2. Designate a Cybersecurity Coordinator to be available 24/7
3. Review current cybersecurity practices and identify any gaps as well as related remediation measures and report those to TSA within 30 days
This final directive relates back to the March 2018 (updated in April 2021) Pipeline Security Guidelines — which were only recommendations. This directive implies they will now become mandatory. This is likely the most significant part of the order as it begins a regime of more compliance requirements. These recommendations are a relatively comprehensive list of security controls and will likely require significant effort for many pipeline operators to achieve.
Perhaps most importantly, the directive makes clear that this is the first step in what is likely to be a more extensive set of requirements over the coming months.
How to review the current pipeline cybersecurity practices?
As mentioned, TSA released a set of security guidelines in 2018 and then updated in April of 2021. These guidelines will form the basis of any review for pipeline operator. So, the first question is: what are the cyber security controls included in the current TSA pipeline recommendations?
TSA constructs its recommendations into the same categories as the NIST Cybersecurity Framework of Identify-Protect-Detect-Respond-Recover. TSA then narrowed the traditional NIST components to a more targeted set of controls that are relevant for converged cyber-physical systems such as pipelines. The current list of controls will be a challenge for many pipelines to achieve efficiently and effectively.
The list of controls includes both procedural and technical requirements. They do not distinguish between IT and OT systems. But the implication is that the guidelines should apply to both, with any necessary adjustments for the OT environment.
The first step against this is to conduct an assessment against these guidelines. The best means for this is a technology-enabled assessment that allows the operator to get visibility into the actual assets, networks and information of the environment. This approach can be accomplished quickly, but importantly provides not only the gaps and roadmap but also the capability to begin remediation immediately rather than to wait for several months to implement tools and technology to remediate.
Steps to achieve pipeline security compliance with the DHS recommendations.
Beyond the assessment, the question becomes how to make progress in overall security maturity. Many operators have not taken programmatic cyber security measures over the past 3 years since the original recommendations came out. Others have taken some steps such as segmenting IT from OT or implementing intrusion detection and/or creating employee cyber security awareness programs. Few will have a comprehensive approach to the controls listed above. Therefore, how should operators go about addressing compliance with these new requirements?
1. Begin at the beginning with a robust asset inventory.
All of the controls included in the list are grounded in the foundation of a robust asset inventory. That inventory is much more than knowing what hardware devices are on your network. It becomes the source of truth for a large portion of the rest of the requirements: software inventory, patch status, status of antivirus signatures, configuration settings and compliance with secure settings, etc. One common situation with users is that they use a network monitoring tool to get asset visibility. However, the “visibility” gained doesn’t provide the depth of inventory of software, users, accounts, patch status, etc. required by these compliance standards.
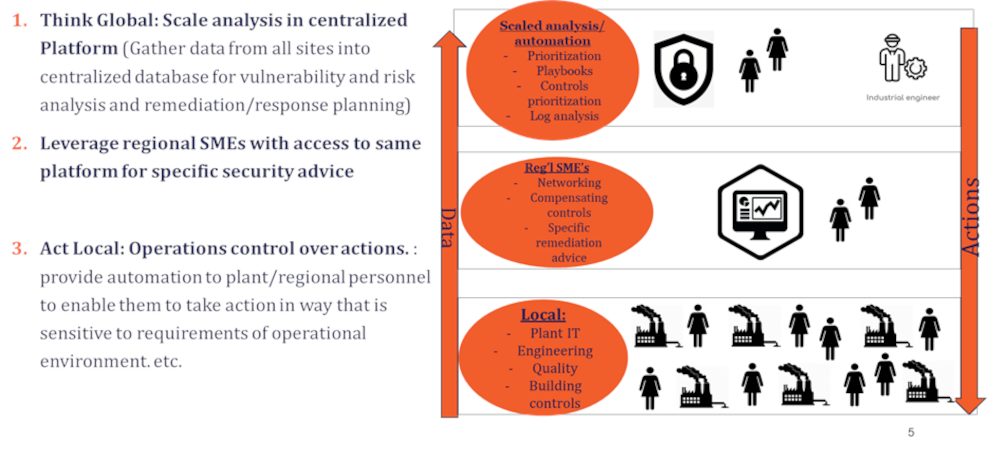
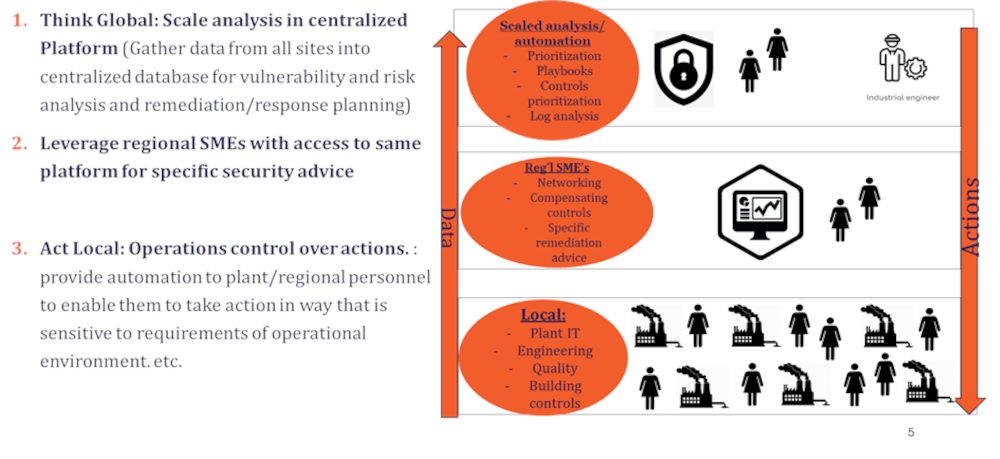
2. Think Global-Act Local.
Compliance with the DHS controls is only partially a “security” challenge. For the most part, it is an operational or labor challenge. When asked for the biggest barrier to securing cyber physical systems, IT and OT leaders list availability of talent as the number one challenge – significantly more than budgets or technology or any other barrier. Verve has been helping customers with compliance for the North American Electric Reliability Corporation Critical Infrastructure Protection (NERC CIP) or other controls regimes for almost 15 years. Efficiency of approach separates the successful ones from the less successful.
To achieve these controls, therefore, requires an approach Verve calls “think global-act local”. This approach centralizes the key data, analysis and reporting across all assets and all security controls in a single enterprise database. This is necessary given the limited number of security knowledgeable resources within organizations. But these controls don’t only call for information and monitoring. They require actions such as patching, user and account management, configuration hardening, etc. These actions, in sensitive OT environments, can cause operational disruptions. Therefore, the approach must enable “act local” when security actions need to be taken. This requires personnel that understand the process and it’s sensitivities to be certain actions are executed in alignment with process. This “think global-act local” approach enables efficiency and operational resilience required in cyber physical systems.
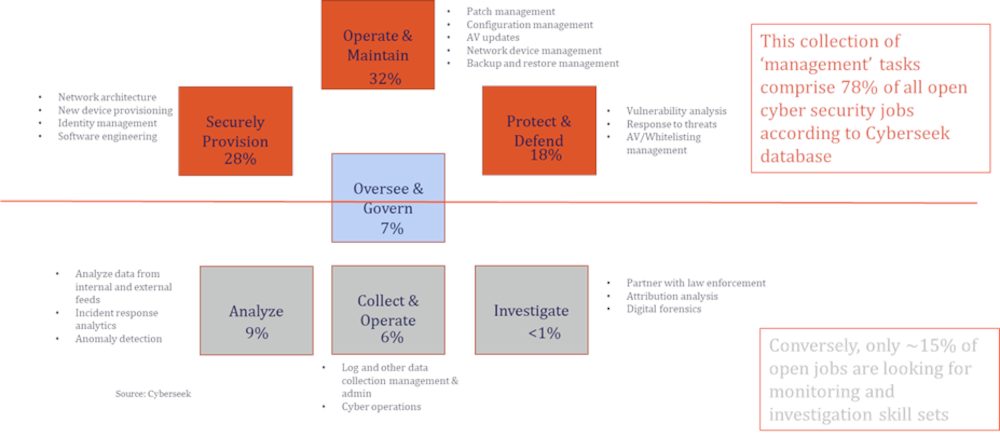
3. Focus on OT Systems Management skill development
Still one of the questions Verve is asked most often is “where do we find the right people for IT-OT cyber security?“ It is critical not to be distracted by the “shiny object” of fancy cyber security “artificial intelligence“, “machine learning” and/or the fancy names used by cyber security researchers like “fancy bear” and “xenotime” etc. The key to achieving improved security maturity and compliance with the controls is OT systems management (OTSM). OTSM is a set of practices similar to those on the IT side. Patch management, vulnerability management, configuration management, user and account management, etc. In fact, according to the Cyberseek database from NIST, over 75% of the jobs in cyber security are systems management jobs, rather than fancy advanced analytics or threat hunting. The good news is these skills are more available and they can be developed more easily within an operational organization. Furthermore, these skills can be automated more effectively.
4. Automate, Automate, Automate
Per the above, many of these tasks can be automated. To achieve maturity with these controls efficiently will require automation. Tools (such as Verve or others) can enable these security tasks to be automated. Practically no organization can afford to achieve security requirements manually.
What’s next for Cyber Security and Pipeline Operators
May 27, 2021 marked the beginning of what will be a significantly greater regulatory regime for pipeline operators. The initial set of recommendations that are now requirements will require a new approach from many pipeline operators to achieve. Verve stands ready to help our nation’s infrastructure operators increase their cyber security maturity and readiness with our combination of software and services.
– This article originally appeared on Verve Industrial’s blog. Verve Industrial is a CFE Media content partner
Original content can be found at verveindustrial.com.
Do you have experience and expertise with the topics mentioned in this article? You should consider contributing content to our CFE Media editorial team and getting the recognition you and your company deserve. Click here to start this process.