The U.S. Department of Defense (DoD) remains committed to safeguarding sensitive national security information by protecting the defense industrial base (DIB) from increasingly frequent and complex cyberattacks. The agency recently released its CMMC 2.0 framework based on 850-plus public comments in response to the interim DFARS rule. The new framework simplifies the program and improves overall governance. While the framework has further optimized the number of controls needed, it hasn’t compromised its focus on “maturity.” In spirit, doing a few things well first is better than trying to spend resources on many things without assurance of quality across all.
The key differences and implications for contractors are summarized in the following table:
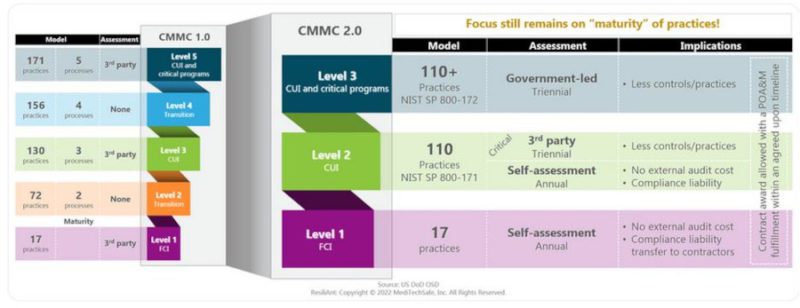
The number of practices/controls required for certification have been reduced for many contractors that are exposed to CUI. This should result in overall cybersecurity and compliance cost reduction.
Contract awards are possible with a Plan of Action and Milestone (POA&M) and commitment to achieving the milestones in an agreed-upon timeline as opposed to needing certification to bid on a contract.
Eliminating third-party assessments for Level 1 and a subset of Level 2 certification-requiring contractors can reduce cost associated with an external audit for those who have internal capabilities of performing assessments in compliance with the CMMC Assessment Guide. A CMMC self-attestation is a representation that the offeror meets the requirements of the CMMC level required by the solicitation. The self-attestation essentially brings the accountability and associated liability to the contractors for ensuring assessment to the CMMC standard and compliance with the requirements. There is a difference between CMMC assessment and “Basic Assessment,” as defined in DFARS clause 252.204-7020, NIST SP 800-171 DoD Assessment Requirements. The Basic Assessment results in a confidence level of “Low” in comparison to what’s required under the CMMC assessment. Contractors wishing to pursue the self-assessment and self-attestation route should be mindful of the differences and resulting liabilities.
The new framework reduces unnecessary reliance on roles, entities and certifications such as RP, RPO, LPP and LTP that were created by CMMC-AB. The program will use CMMC-AB-certified CMMC third-party Assessment Organizations (C3PAO) and CMMC Assessors and Instructors Certification Organizations (CAICO), provided that CMMC-AB is ISO/IEC 17011 compliant. Level-3 assessments will be government led, and the government can potentially contract with a C3PAO or other entities. The DoD will govern and likely approve how and when a CMMC assessor can engage with contractors.
While CMMC 2.0 appears to have eliminated all maturity processes, the spirit of maturity is still intact within the assessment procedure. The assessment procedure involves evaluating specifications, mechanisms, activities and individual(s) associated with each CMMC practice for the assets in scope. The assessment methods include examining documentations (provides evidence of intent), interviewing staff (evaluates the belief of existence) and testing (provides a validation of existence and effectiveness). In a case where an entity inherits a practice objective, an assessor will have to provide adequate evidence of the effectiveness of the practice in that entity via testing. While a certified assessor is not required to use all objects and methods, s/he can use all of them to gain confidence that the CUI requirements have been satisfied. In other words, the assessor can assess for maturity level up to five processes (i.e., having KPIs, noting improvements and reporting mechanisms to the senior executives for high-risk items) for CMMC Level 3 certification. Assets include all things of value such as people, processes, systems, organizations, etc., and they are considered to be in scope if they can process, store or transmit CUI, connect to CUI assets or provide security function.
The subcontractors will be assigned the same CMMC level as the prime contractors if they are handling the same type of FCI and CUI. In cases where the prime only flows down select information, a lower CMMC level may apply to the subcontractor.
In summary, CMMC 2.0 really doesn’t change the need for rigor in cybersecurity from DIB. It reduces some practices and hence the associated costs; it offers some flexibility by allowing an organization to win a contract with POA&M and performing self-assessments where appropriate. There is no reason for companies to wait for an official rule to follow the framework for at least up to Level 2 (Level 3 details are yet to be confirmed) certification. We know that hackers have been targeting aerospace and defense industries for years. Early adoption of the framework will ensure robust enterprise cybersecurity and put them ahead of the game with DoD contracts. Overall, CMMC 2.0 remains focused on maturity, simplifies the program, streamlines governance and potentially reduces cost of compliance.
Do you have experience and expertise with the topics mentioned in this article? You should consider contributing content to our CFE Media editorial team and getting the recognition you and your company deserve. Click here to start this process.








