On Sept. 29, 2020, the U.S. Department of Defense (DoD) released an interim rule to amend the Defense Federal Acquisition Regulation Supplement (DFARS) to implement a DoD assessment methodology and cybersecurity maturity model certification (CMMC) framework to assess contractors’ implementation of cybersecurity requirements for public comments. While cybersecurity requirements have been a part of the defense procurement process in the form of NIST 800-171 compliance for some time now, according to the release:
- “Findings from the DoD Inspector General report indicate that DoD contractors did not consistently implement mandated system security requirements for safeguarding CUI (controlled unclassified information),”
- The current compliance requirement “does not provide the DoD with sufficient insights with respect to the cybersecurity posture of Defense Industrial Base (DIB) companies throughout the multi-tier supply chain for any given program or technology development effort,” and
- The “NIST SP 800-171 per DFARS clause 252.204-7012 does not sufficiently address additional threats to include advanced persistent threats (APTs).” Hence, the department needs “a risk-based cybersecurity framework for the DIB sector, such as CMMC, as the basis for a mandatory DoD standard.”
Outcome of CMMC compliance
While the DoD’s goal is to ultimately have all contracts comply to CMMC, the phased rollout process, effectively starting in about 90 days, includes a two-pronged approach in the interim to ensure the DIB’s ability to protect federal contract information (FCI) and CUI. The timeline to implement CMMC across the DoD contractor population will be approximately seven years. The interim two-pronged approach includes:
1. CMMC:
The contracts mandating CMMC compliance will require a contractor to have the certification in place at the time of award. Therefore, the contractors who have seen CMMC requirements in request for information/request for proposal (RFI/RFP) should start the gap assessment process against CMMC requirements now, remediate the gaps and demonstrate process maturity to gain certification. They should also ensure that their supply chain is compliant.
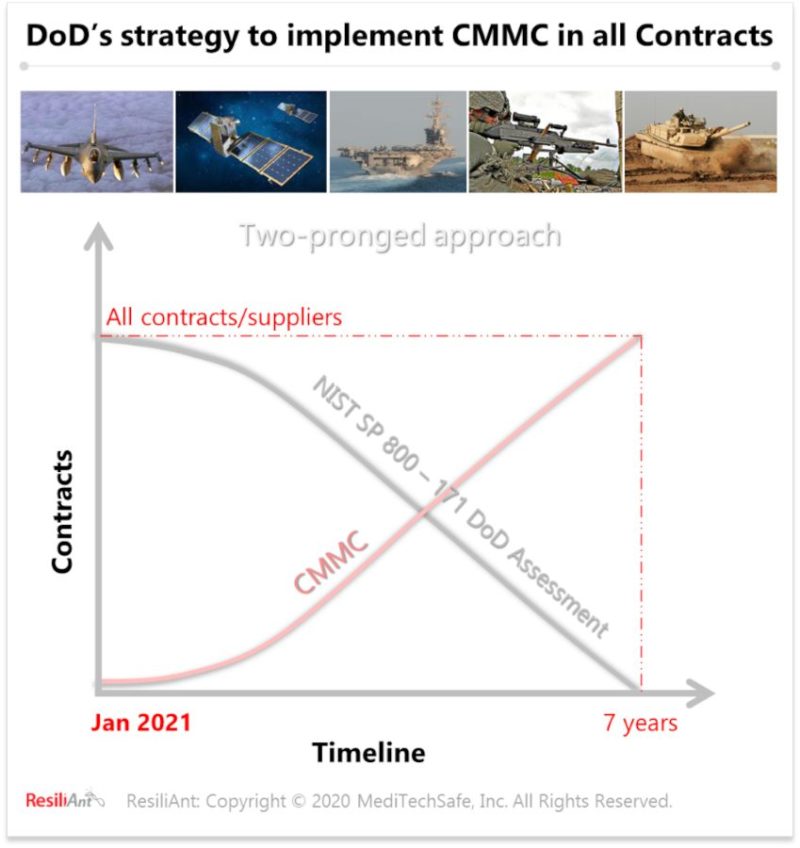
2. NIST SP 800 – 171 DoD assessment methodology:
The contracts not requiring CMMC will require contractors to comply to one of the NIST SP 800-171 DoD assessment levels (basic, medium, high) based on the criticality of the information. These contractors will be required to upload their assessment scores, dates of assessments, descriptions of required remediation actions and expected dates of completion along with their respective commercial and government entity (CAGE) numbers onto the Supplier Risk Management System (SPRS). While contractors requiring basic level assessments can perform the assessments themselves and upload the required information onto the SPRS, others will have to support government-performed assessments with evidence and documentations.
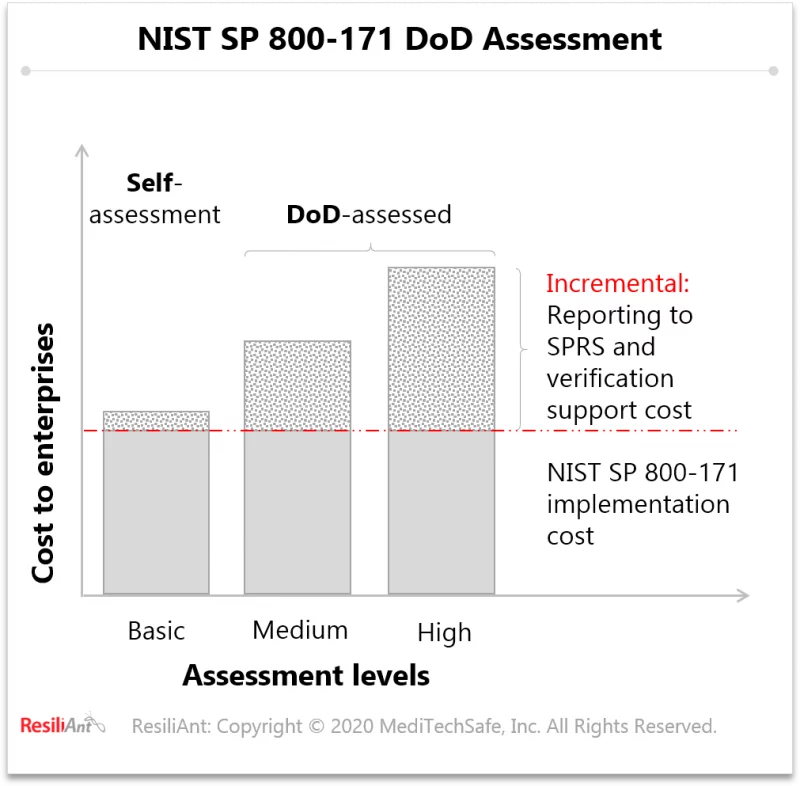
In essence, the DOD is enforcing rigor on cybersecurity risk management efforts within the DIB. Except for the organizations requiring a basic level of assessment, all others will have some degree of an external audit. It is in the best interest of all organizations to ensure information integrity, rigor, consistency and cost productivity in their cybersecurity risk management efforts. They should start their efforts toward CMMC as early as possible; it will not only make the transition to CMMC smoother but also improve their enterprise risk management in a cost-effective manner.
– This article originally appeared in Resiliant’s Knowledge Center. Resiliant is a CFE Media content partner.
Do you have experience and expertise with the topics mentioned in this article? You should consider contributing content to our CFE Media editorial team and getting the recognition you and your company deserve. Click here to start this process.