
New Sonar platform could help prevent phishing attacks
Sonar is a new AI-enabled browser extension designed to help detect phishing emails and enhance cybersecurity

Sonar is a new AI-enabled browser extension designed to help detect phishing emails and enhance cybersecurity

The top 5 articles from August 2023 covered how to build an effective cyber strategy and the government impact on OT cyber risk.

Lesley Carhart talks about working in incident response, a power plant that turned on by itself and the maturity journey of OT cybersecurity.

Biometric data is a valuable target for cybercriminals, and hacking of this type of data is becoming a popular manner of identity theft.

ICS Pulse talked to Dr. Jesus Molina about the physical consequences of cyberattacks and what it means for your industrial environment.

Debbie Gordon, of Cloud Range, discusses the dangers of human vulnerabilities and why cyber practitioners need to have more than just skills.

Water and wastewater is critical to national security, economic stability and public health. Here’s how to protect it from cyber threat.

Thomas Pace discusses the prevalence of ransomware, the danger of supply chain attacks and how SBOMs can help secure systems.

Bot attacks on industrial control systems are becoming a focal point, as they are capable of causing harm to critical infrastructure.
In 2022, Canada’s SickKids hospital was hit by LockBit ransomware, which impacted its internal systems, phone lines and website.

Sonar is a new AI-enabled browser extension designed to help detect phishing emails and enhance cybersecurity

The top 5 articles from August 2023 covered how to build an effective cyber strategy and the government impact on OT cyber risk.

Lesley Carhart talks about working in incident response, a power plant that turned on by itself and the maturity journey of OT cybersecurity.

Biometric data is a valuable target for cybercriminals, and hacking of this type of data is becoming a popular manner of identity theft.

ICS Pulse talked to Dr. Jesus Molina about the physical consequences of cyberattacks and what it means for your industrial environment.

Debbie Gordon, of Cloud Range, discusses the dangers of human vulnerabilities and why cyber practitioners need to have more than just skills.

Water and wastewater is critical to national security, economic stability and public health. Here’s how to protect it from cyber threat.

Thomas Pace discusses the prevalence of ransomware, the danger of supply chain attacks and how SBOMs can help secure systems.

Bot attacks on industrial control systems are becoming a focal point, as they are capable of causing harm to critical infrastructure.
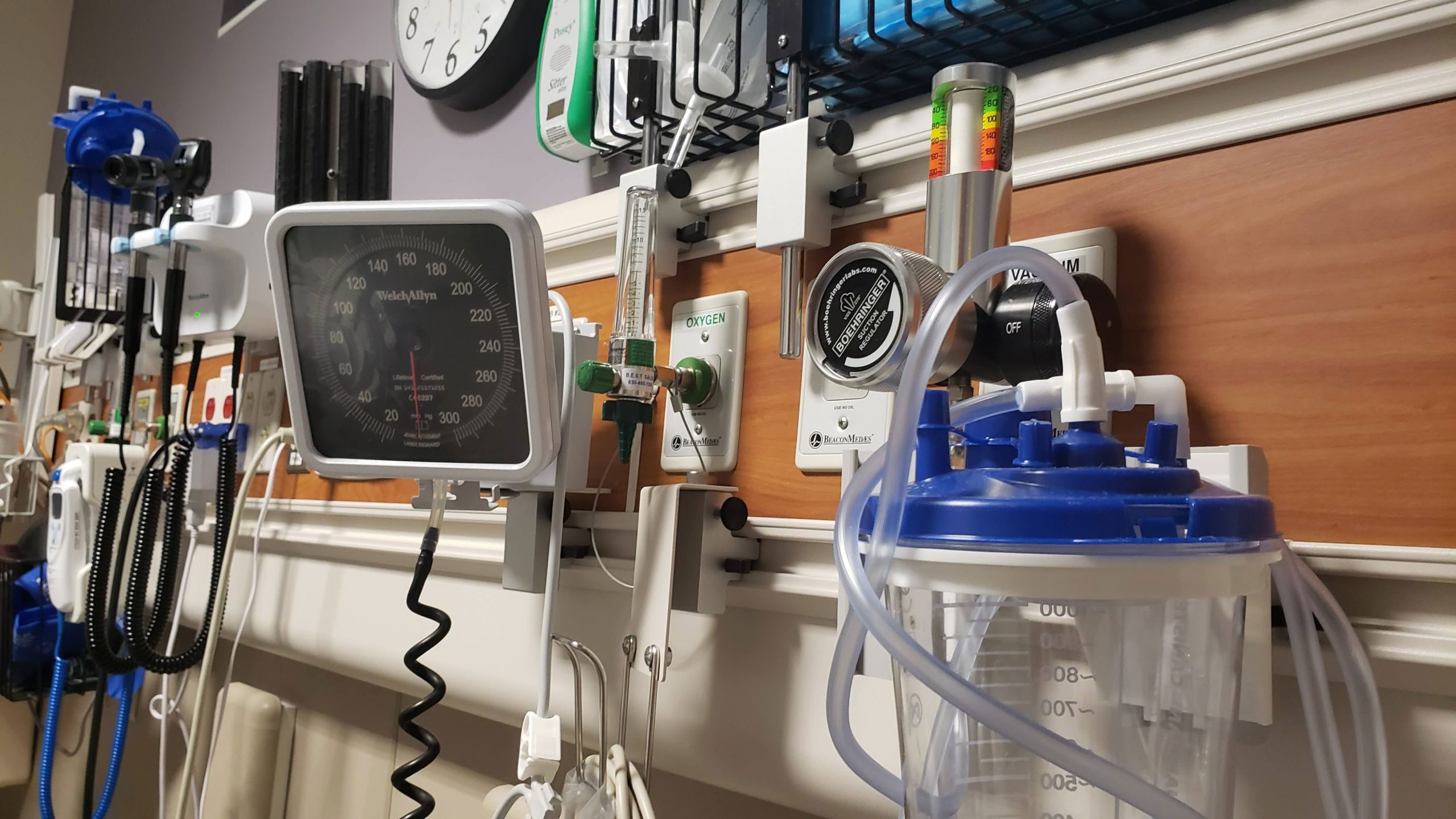
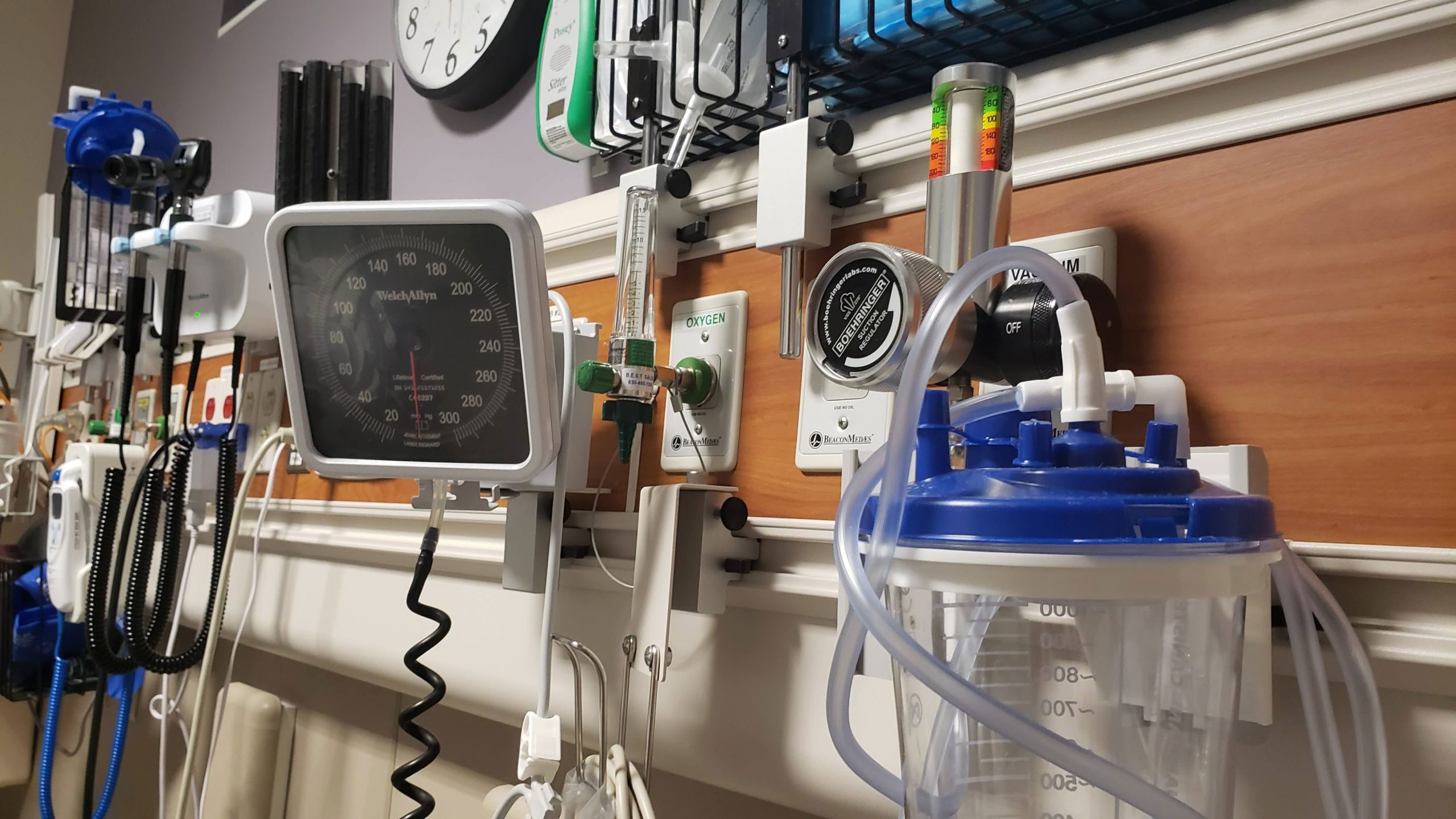
In 2022, Canada’s SickKids hospital was hit by LockBit ransomware, which impacted its internal systems, phone lines and website.
Keep your finger on the pulse of top industry news

This website uses cookies so that we can provide you with the best user experience possible. Cookie information is stored in your browser and performs functions such as recognising you when you return to our website and helping our team to understand which sections of the website you find most interesting and useful.
Strictly Necessary Cookie should be enabled at all times so that we can save your preferences for cookie settings.
If you disable this cookie, we will not be able to save your preferences. This means that every time you visit this website you will need to enable or disable cookies again.