Automation of critical infrastructure continues to add efficiencies, and cybersecurity measures help protect those assets. Understanding the anatomy of an attack through its lifecycle can help with cybersecurity, especially with an industrial control system (ICS).
Critical infrastructure is defined as: “…the systems, networks and assets that are so essential that their continued operation is required to ensure the security of a given nation, its economy, and the public’s health and/or safety.”
These systems include the electrical power grid, oil and gas pipelines, telecommunications and broadband systems, and water and wastewater treatment systems, to name a few. Given the definition above, critical infrastructure spans a large spectrum of goods and services that make our lives healthy, comfortable and safe. As one would expect, these systems and services would be prime targets for adversaries who would seek to disrupt society to further some ends.
It is obvious that critical systems must be protected, but many questions arise: what systems must be protected and in what priority?
Know the cyber kill chain
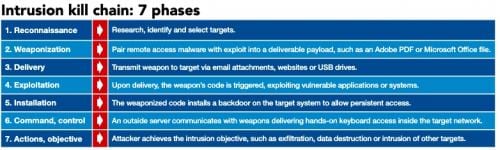
The “cyber kill chain” is a model developed by Lockheed Martin to describe the steps of a cyber attack from its earliest stage, reconnaissance, and to its final stage: data exfiltration. The kill chain has distinct steps that describe each stage of a cyberattack lifecycle.
The kill chain model helps in understanding how attacks are perpetrated and prepare us to deal with attacks such as ransomware and security breaches. An attack typically follows an ordered sequence of penetration techniques; using the Lockheed model, these steps are:
1. Reconnaissance: This stage involves planning, observation and research of and into a prospective target. Some tools are social media, such as Facebook and LinkedIn, which are used to gather personal information or detailed information about a company. By observing a target online (or by any other means) the attacker builds a profile of the target and can design the most effective tactics for perpetration of the attack. Most often, phishing emails are used against the target that have been designed around the information gathered about the target during the recon stage. Other attack vectors are designed based upon software penetration methods, such as port scanning or brute force password attacks. By far the most effective vector is the compromise of the human asset.
2. Intrusion: Using the information gathered and analyzed in the recon stage, the attacker breaches the network and installs malware or a reverse shell program, which allows unfettered access to the target network. At this stage of the attack, the goal is to look around the network for additional vulnerabilities to exploit. The network is mapped from the inside and assets such as credential files are located and cataloged for future attacks.
3. Exploitation: Based upon the information gathered during the intrusion stage, the attacker can then exploit the vulnerabilities found in the systems. At this stage weaponized code can be dropped on servers and the attacker can obtain sensitive data such as password files, certificates, or even RSA tokens. Once inside the network, there is almost nowhere the attacker cannot go. If the attack has proceeded to this stage, the system is compromised, and data is at risk. In attacks on critical infrastructure, control systems have likely been compromised and malware is resident in critical systems. The attacker can hold data or systems for ransom or wreak havoc on the target system.
4. Privilege escalation: Using data gleaned from exploitations of system vulnerabilities, the attacker will use stolen credentials to obtain higher permissions to access higher security systems or file areas. This escalation allows the attacker to obtain more secure and sensitive data because of their escalated privileges on the compromised system. The attacker also can access protected systems requiring high-level privileges to access.
5. Lateral movement: With higher-level access, the attacker can move through the target system, exploring other connected systems and file locations, searching for caches of sensitive data that can be exploited, allowing an even higher escalation of privileges, acquisition of higher permissions, and greater access to critical systems.
6. Obfuscation: To perpetrate a successful attack, the attacker covers their tracks by several methods. Data compromise methods include altering it to remove any evidence of compromise, planting false data trails that lead nowhere in the system, and clearing operating logs are effective and useful means to foil network forensics. The goal at this stage is to obscure or remove any evidence of the attack and thereby avoid attribution and countermeasures. Many attacks have remained undetected for years before being discovered, most often by accident.
7. Denial of service: Another method for preventing detection is to shut the system down by various means, or to destroy data on a mass scale. This is very effective in obscuring an attack, but is very destructive, resulting in the loss of real property. In critical infrastructure, this stage of the attack, such as shutting down critical servers or the entire electrical grid, as was done in the Ukraine in 2015, can be very disruptive.
8. Exfiltration of data/payload: If the goal was to obtain sensitive data, this stage is where the data is removed from the system. If the attack was successful, then the attacker will have obtained the target data and disappear, leaving the information technology (IT) staff picking up the pieces and engaged in the long process of rebuilding the network. In critical infrastructure, this stage is when the objective is executed and the payload is delivered against the target.
Other kill chain models
A kill chain is a threat model that can be used to analyze possible attack vectors and allow the design of countermeasures to mitigate the threats they pose to an organization. The Lockheed Model is based upon the military kill chain model (F2T2EA: find, fix, track, target, engage, assess), but there are also other models that are more focused on specific attack landscapes such as within an ICS.
These models are useful as a tool in developing cyber defenses through gaining an understanding of how attacks are perpetrated. The Gartner Model, the MITRE ATT&CK framework, The SANS ICS Cyber Kill Chain, and the Unified Kill Chain are four variants on established kill chain models that also can be used to understand and mitigate attacks on critical systems. The figure below is an example of a kill chain model that introduces the concept of “Command and Control” or “C2,” which gives the attacker complete control of the compromised system.
Mining data to enable breaches
The attacker relies on initial accurate recon of the intended target and the identification of the most vulnerable part of that system to design the most effective attack. Most often it is the human asset and the vast trove of data obtained from intelligence gathering techniques such as open source intelligence, or OSINT (social media particularly) and human intelligence or HUMINT, which is exploitation of human relationships through social engineering, that are the two most often used methods of reconnaissance used by threat actors to design means and methods to enable them to breach a system.
The volume of sensitive data that can be found on the internet by a diligent and skilled researcher using specialized tools is almost limitless – mining this data for the purpose of exploitation is a skill that is highly valued. In the hands of a skilled operator, this data becomes the basis for a successful social engineering attack – and beyond.
Critical infrastructure cybersecurity: A guide to understanding
The world is intimately connected on many levels, and with greater connections are greater needs for cybersecurity. In the history of the world, we have never been more connected; in fact, our level of connection has reached near cybernetic proportions. The average human may be connected with the world 24/7.
It is considered unusual that one does not have a phone or that it is turned off. Constant communication has become normal. We have become one with the machine. Mass communication on a mass scale affords the opportunity to effect massive change. We are technology-enabled humans, nearly cyborgs in function; our lives, and our well being, depend on electronic communications.
We are also an automated world and becoming more automated daily. Automation, when appropriately implemented, can enhance lives. While exceptions exist, critical infrastructure derives many benefits from interconnected, secure automation.
Five ways to understand cybersecurity
What are the attack vectors; how do we define an attack surface; what are the methods used and how to design countermeasures; where are the weak spots and how do we mitigate? Describing each of these issues in plain language can help avoid catastrophe.
While myriad elements are present, and volumes continue to be written, cybersecurity can be outlined in five basic parts.
- The cyber kill chain is a model used to understand how a cyberattack is planned and executed.
- The human element is the weakest link in the system and typically the first asset compromised in an attack. Social engineering strategies can be made less effective.
- Lesser-known attacks on critical infrastructure have caused loss of life, property or wealth.
- Attack execution provides understand of what’s happening, even when hidden.
- Countermeasures and situational awareness can be considered for implementation.
Various resources of greater length and depth are available beyond information here, but this provides a good foundation for more study.
Cyber attack lifecycle info
Further reading on the concepts of the Cyber Kill Chain includes the following:
- The Unified Kill Chain, Paul Pols
- A “Kill Chain” Analysis of the 2013 Target Data Breach, U.S. Senate Committee on Commerce, Science and Transportation
- Intelligence-Driven Computer Network Defense Informed by Analysis of Adversary Campaigns and Intrusion Kill Chains, Lockheed Martin
- The MITRE ATT&CK Framework: https://attack.mitre.org/
- Analysis of the Cyber Attack on the Ukrainian Power Grid, SANS ICS, E-ISAC
Daniel E. Capano is senior project manager, Gannett Fleming Engineers and Architects, and on the Control Engineering Editorial Advisory Board. Edited by Mark T. Hoske, content manager, Control Engineering, CFE Media, [email protected].
KEYWORDS: Cybersecurity, cyber attacks, cyber kill chain
The cyber attack lifecycle or cyber kill chain, help with understanding cybersecurity measures.
More than one cyber kill chain model is available.
Data mining helps enable cyber attacks.
CONSIDER THIS
Are you offering information to help others attack your organization?
See additional threats and vulnerabilities stories including:
Five steps to improve OT, ICS cybersecurity awareness in manufacturing
Cyberattacks on SolarWinds and Oldsmar: CEO Interview Series, John Livingston, Verve Industrial Protection
Original content can be found at Control Engineering.
Do you have experience and expertise with the topics mentioned in this article? You should consider contributing content to our CFE Media editorial team and getting the recognition you and your company deserve. Click here to start this process.








